Manage organization users
Learn how to manage users in your Retool organization.
Retool provides several options for admins to add users to their organization:
- Invite users to sign up with an email address and password.
- Allow users to request access to your organization.
- Specify a list of domains to automatically add users with matching email addresses.
- Configure SSO and allow users to sign in using your SSO provider.
- Receive notifications about suggested users.
You can also disable users to prevent them from accessing the organization at any time.
Invite users
Users needing to sign in with an email and password must first be invited to a cloud organization. If they attempt to sign up first, Retool creates a new organization and adds them to it.
You can invite users to join your Retool organization. New users can create an account with their email address and password, or sign in using SSO.
To invite a user:
- Click the User menu on the upper-right, then select Settings.
- Select the Users settings in the User management section of the sidebar.
- Click Invite, then enter the email addresses of users to invite.
- Retool sends an invite URL to the users you specified. This URL expires after one week.
Admins can also invite users directly from an app by clicking Share.
For organizations on the Enterprise plan, users can sign up using the URL of your deployment's sign up page.
Retool strongly recommends disabling signups and enforcing SSO usage.
Allow users to request access
To enable users to request access to join your Retool organization, go to Settings > Advanced Settings and toggle Allow anyone to request to join.
Enabling this settings adds a link to your organization login page (<your_subdomain>.retool.com/auth/login>) prompting users to enter a valid email address.
Visit Settings > Users to approve an access request. After approving, the user receives an email to join your Retool organization.
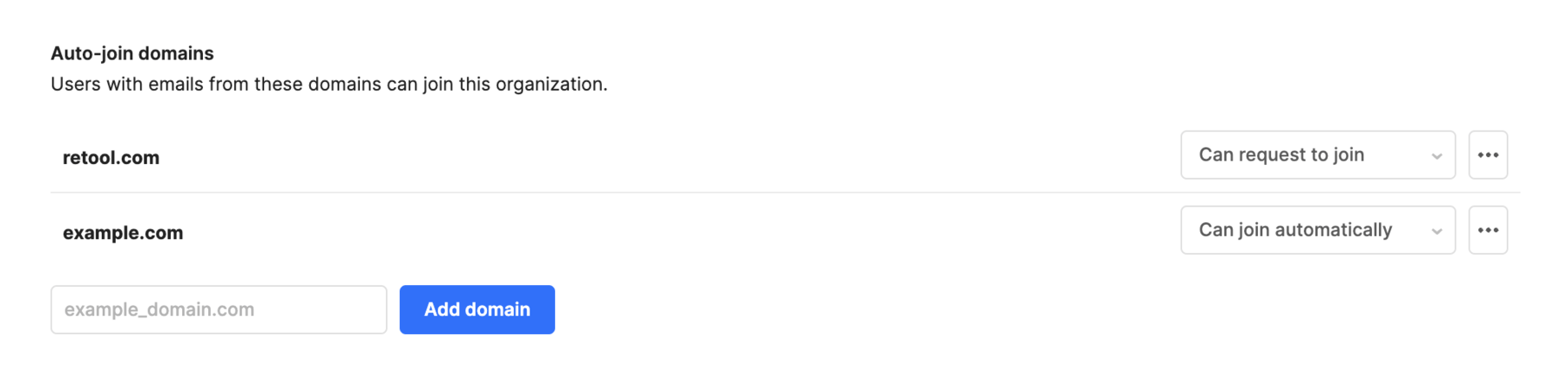
Configure auto-join domains
Cloud organizations can specify a set of domains from which to allow users with a matching email address to join. Navigate to Settings > Advanced Settings, then add one or more domains to the Auto-join domains section. You then specify whether users with a matching email address can either request to join or join automatically for that domain.
Auto-joining domains is not supported for self-hosted instances.
Add SSO users
Retool supports Sign in with Google on all pricing plans on cloud instances. Organizations on the Enterprise plan can configure other supported SSO providers, such as Okta.
If you have a cloud instance and use Google Workspace, all users who share the same domain can select Sign in with Google and log in. Users are automatically added to your organization.
Organizations on the Enterprise plan can configure additional SSO providers. Users can then sign in automatically, but additional steps are required before they have access.
You can generate an auto-join link from a mobile app's share options that allows users to sign up directly from the Retool Mobile app using SSO. Users who sign up using this method are added as mobile-only users. You must configure auto-join domains to enable this option.
Suggest users
Retool users who aren't administrators can notify admins about users who might need access. To suggest a user, navigate to Settings > Users and click Suggest. Users can provide email addresses for potential users and click Suggest new members.
Retool organization admins receive a notification and can decide whether to add or invite users.
Disable users
Retool organization admins can disable access of any user within their Retool organization. Disabling users prevents them from logging into their Retool account, as well as accessing or editing any apps, queries, or resources in your shared Retool organization.
You can disable users from your organization's Users settings. Select a user, then click Disable user.
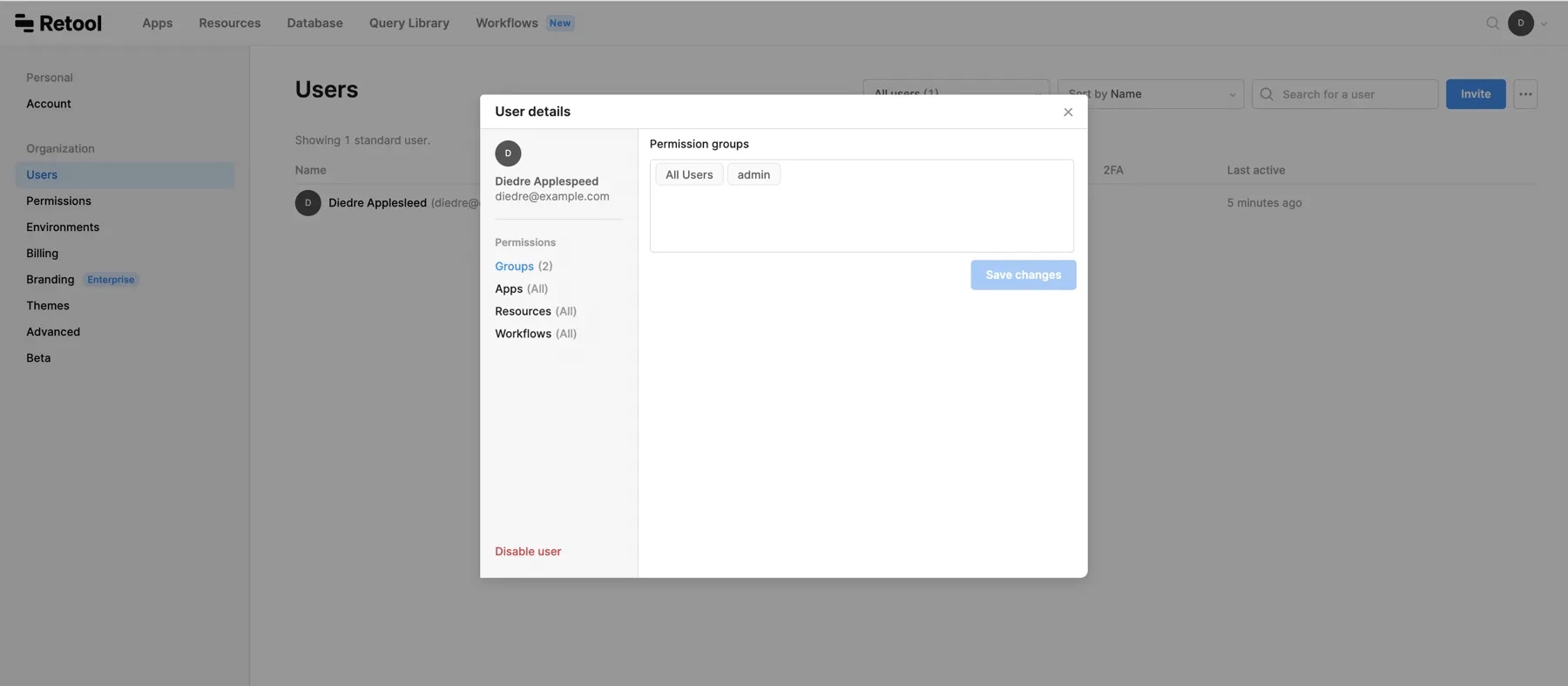
You can enable a disabled user by clicking ... next to their name, then Enable user. If you don't see the disabled user in the users list, ensure Hide disabled users is not selected in the user filters.